Apache SSL CSR Generation instructions
This document provides instructions for generating a key pair and CSR for an ApacheSSL server.
Apache and OpenSSL
You will need to make sure that you have OpenSSL installed on your Web Server.
If your server is *nix or Linux, you can get OpenSSL from: https://www.openssl.org/source/
Please view the documentation on these sites for instructions on how to install OpenSSL onto your web servers.
Generating a Key Pair using OpenSSL
Go into the directory that you are going to generate your key pairs in.
cd /usr/local/apache/ssl.certs/
And then run the following command:
openssl genrsa -aes256 2048 > server.key
This command will generate a 2048 bit RSA key pair and will encrypt the private key using AES256 encryption based on a pass phrase you have to enter. See the following screenprint.
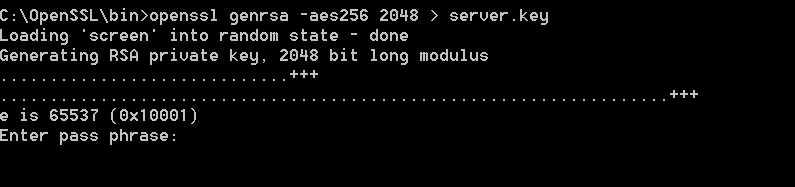
It is important to remember the pass phrase. Without the pass phrase you will not be able to use the private key or certificate based on this keypair.
Generating a CSR using OpenSSL
The second openssl command will generate a Certificate Service Request (CSR) based on the key pair generated in the previous step.
openssl req -new -key server.key -out server.csr -sha256
First openssl will ask you to enter the passphrase. From there OpenSSL will ask you a series of questions that you will need to answer.
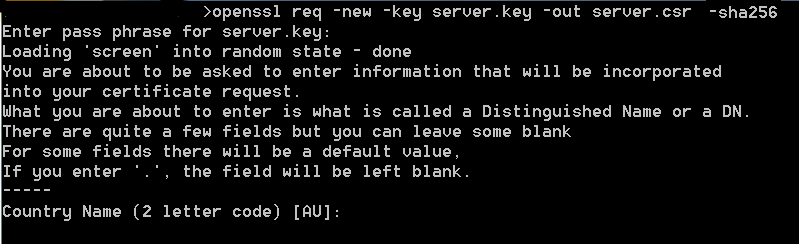
KPN will not use this information and will only include validated information in the certificate. This information is part of the webform to request a server certificate. It is highly recommended to fill in the CommonName (CN) in the CSR for the purpose of reference. This ensures it is always easy to determine for which system a specific CSR was created.
You also will want to make the file only readable by the administrative account (*nix).
#chmod 400 server.key
You have now created the Key pair that you will use for your server.
You can now go to the certificate request page and use the CSR that you created. You just need to open up the CSR file in a text editor that does not add extra characters (e.g. notepad) and past it in the webform.


